
Metal Detectors and Chocolate
June 15, 2017The world absolutely loves chocolate and in North America we eat more of it than any other country in the…
How to Make Your Home Intruder-Proof – Pokemon Go Style
October 4, 2016Pokémon Go has been in the news over the past few months, for a mixture of positive and negative reasons.…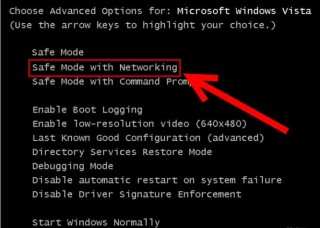
How to Completely Remove Samas Ransomware from Windows?
April 28, 2016Looking at the way the last few months have panned out it won’t be an exaggeration to state 2016 as…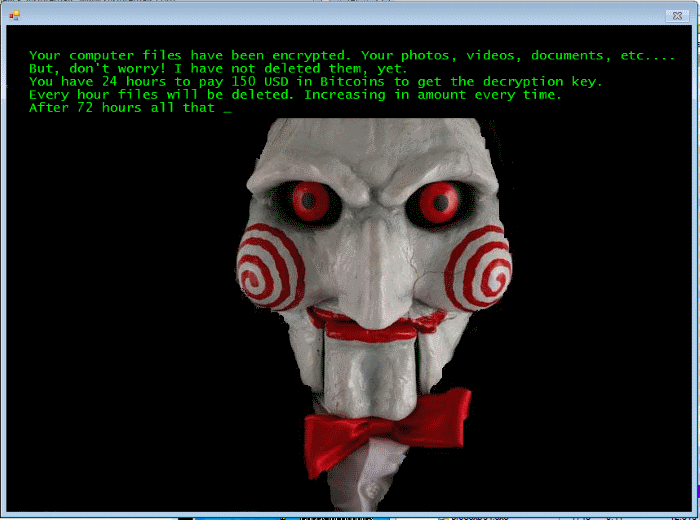
New Crypto-Ransomware JIGSAW Plays Nasty Games
April 21, 2016Crypto Ransomware has been progressing immensely in recent weeks and now it has taken a massive step in order to…
Top 15 Best Free Keylogger Softwares to Monitor Keystrokes in Windows
March 11, 2016In order to check the keystrokes that are typed on the keyboard, record the passwords and encrypt sensitive information, certain…
What Is Ransomware And How Can You Protect Against It?
March 2, 2016In the past decade more and more hacking solutions have emerged, all of which targeted important data systems and personal…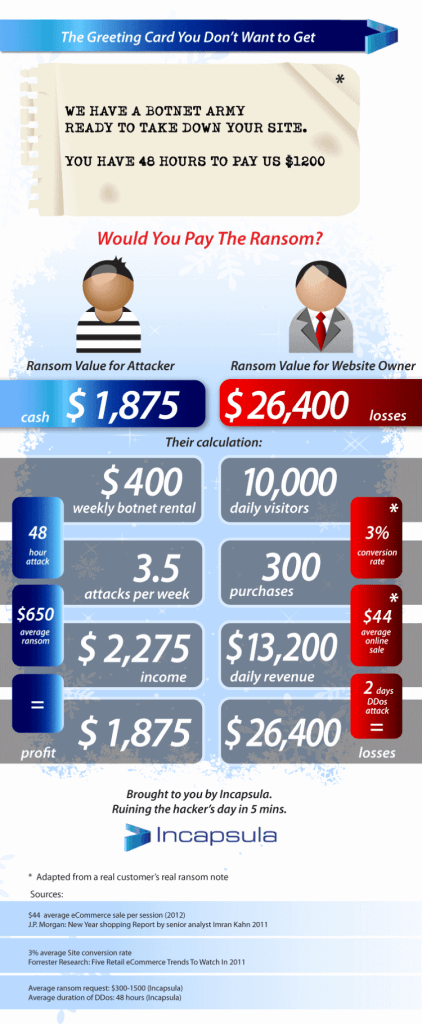
Booters and Stressers: What you need to know about DDoS for hire?
May 22, 2015Think back to when you were a kid. No matter how well-adjusted and even-tempered you were (or weren’t) there was…
How Secure Is My Password and Why Should I Care?
April 29, 2014How secure is your password? Probably not very, to be frank. The past few years have seen one security breach…The Danger Of Open Recursive DNS Resolvers
April 14, 2013Last week we issued a call for the DNS, ISP and hosting industries to redouble their efforts to close down…Security Breaches 2012. Lessons To Learn
September 21, 2012The digitalization and mobilization of modern world lead to the situation when we store almost all our personal and business…