The Danger Of Open Recursive DNS Resolvers
Last week we issued a call for the DNS, ISP and hosting industries to redouble their efforts to close down open DNS resolvers. They present a clear danger to our mission of providing fast, stable, and reliable data services to our clients.
Anyone following the tech news in recent days can’t have failed to notice the number of stories concerned with distributed denial of service attacks, the biggest of which was the attack carried out against the popular spam monitoring service, Spamhaus, which creates spammer and spam-enabler blacklists that are used by many in the industry.
We’re used to hearing about DDoS attacks that use co-ordinated botnets to generate packet floods that are directed at target domains in an attempt to knock them off the net. This is the favorite tactic of the Anonymous vigilante group.
Botnets are difficult to build and maintain, relying on existing vulnerabilities that allow machines to be infected with the botnet client. Because they’re difficult to build, botnets are a scarce resource and are expensive to hire for DDoS attacks.
Unfortunately, there is much more cost effective and simple-to-use method of generating large amounts of targeted bandwidth. The large-scale attacks that have reportedly generated 300Gbps of data and strained the resources of some of Europe’s largest service providers produced most of their bandwidth by exploiting poorly configured domain name servers.
Well-configured domain name servers accept requests from a limited range of IPs. Open DNS resolvers will return data to any IP that makes a request. The major benefit for criminals to using DNS servers for their denial of service attacks is that domain name server often return much more data than the original requester sent. A DNS request of 81 bytes may elicit a response of 1499 bytes. A DNS server running DNSSEC can produce a packet 18.5 times that of the requesting packet. With a carefully designed request, it’s possible to have DNS servers dump 100 times more data than the requesting client sent.
This is a very handy for the DDoSer, because they can take advantage of open DNS resolvers to massively amplify the available bandwidth for an attack. If they have 500Mbps per second of bandwidth available, they can prompt insecure DNS servers to send out 50Gbps. All they need to do is spoof the request IP, replacing the IP of the domain that issued the request with that of their target and they can rain fire on any domain on the Internet with minimal resources and expertise.
While not an existential threat for the Internet as a whole, 300Gbps can certainly make things difficult for ISPs and other bandwidth sellers, degrading performance. At DNS Made Easy, we have experienced attacks of more than 200Gbps.
The Open DNS Resolver Project believes there are about 27 million open resolvers on the Internet at the moment. It’s been estimated that fewer than 100,000 of them were used in the Spamhaus DDoS. It’s a worrying situation when one of the biggest denial of service attacks in history used only a fraction of the available bandwidth amplification.
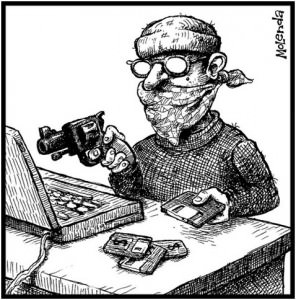
While we are capable of mitigating many of the effects of a sustained DDoS attack, it makes no sense to leave millions of loaded guns in plain sight of malefactors.
Author Bio:- Evan is the technical writer for DNS Made Easy, a leading provider of DNS hosting. Follow DNS Made Easy on Twitter at @dnsmadeeasy, Like them on Facebook http://www.facebook.com/dnsmadeeasy,