
Talking to Kids About Internet Safety
January 19, 2023Many adults today grew up with access to the internet in its infancy, and through experience, they have learned that…
Security Measures For Jira – How To Secure Jira Data?
January 13, 2023Jira has become a critical tool for most of software development companies but is more and more widely used by…
How to Connect Outlook Inbox with Salesforce?
January 5, 2023Integrating Outlook inbox with Salesforce provides sales teams with the ability to manage their email apps and keep up-to-date salesforce…
Telecom Trends: Why Virtual Numbers Have Made Landlines Obsolete
January 3, 2023Communications have changed drastically over the last 10-20 years. Back in the 2000s, the landline was the quickest way to…
Why There Has Never Been a Better Time to Be a Sports Fan
December 28, 2022It’s easy to take for granted many of the conveniences that we get to enjoy in the modern world. Only…
Anonymizers vs Personal Proxies. What’s the Difference? Which is Better?
December 27, 2022Anonymizers and personal proxies both offer a form of online privacy, but the two technologies are quite different. An anonymizer…
10 Tips For Better Password Security
December 15, 2022How often do we reset passwords? Too often? What makes us change our passwords? We frequently change the password to…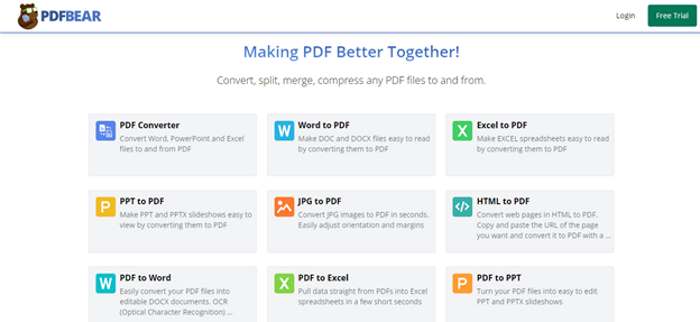
How to Split PDF Online Without Downloading Any App
December 11, 2022If you're tired of using Adobe Acrobat to split your PDFs, this guide is for you. We'll show you how…
Firewalls 101: What is Firewall?
December 8, 2022Monitoring and filtering out the incoming and outgoing network traffic is essential for your organization's network security. You must install…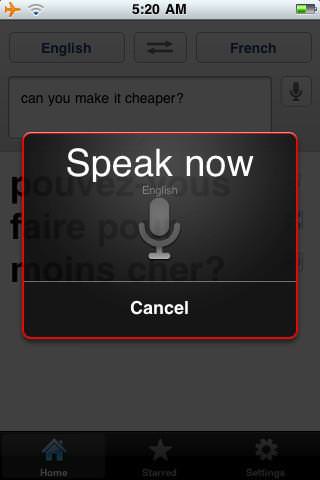
Why Is It Good to Translate Audio Files to Text?
December 5, 2022Audio files, like those of podcasts and radio shows, are an excellent way to reach a wider audience. They allow…