Insider Threats: What They Are, And How to Protect Your Data

In spite of the ostensible widespread recognition of insider threats being serious, the majority of business owners tend to show insufficient follow-through when it comes to deploying a robust, threat-specific data protection strategy. The latest Accenture’s research says 69% of organizations have reported they experienced an attempt, or successful threat of data due to the menace in 2019. At the same time, according to SecurityIntelligence study insider threats account for up to 60 percent of cyber attacks and data breaches, which makes the tendency sound even more shocking… Meanwhile, most cases go unnoticed for months or years in actuality.
So, in this article we’ll try to scrutinize the issue, and answer the most crucial question about data security: what can a responsible business leader do to mitigate the risks associated with data loss due to the insider threats?
What Is An Insider Threat
Basically, insider threats take place when an individual with legitimate access to company assets uses it, whether maliciously or unintentionally, to cause harm to the organization’s critical information, systems, or business itself. Not necessarily that need to be a current employee or officer in the company; former workers, board members, consultants, contractors, third party vendors, or business partners could pose a threat as well.
What are the motives? According to the IBM report, there are two major types of insider threats, namely malicious and inadvertent. The malicious type, as a rule, pursues goals such as
- sabotage
- espionage
- intellectual property theft
- fraud (financial gain)
Inadvertent type, however, is normally centered around accidents or negligence, and includes
- human errors
- phishing
- malware
- stolen credentials
- unintentional aiding (or abetting)
- simple convenience
Nevertheless, despite the primary motivation of the actor, even a slight data leak can lead the company to an impressive amount of losses — which makes it a must for a business leader to learn to detect and prevent insider menaces.
Why Are Insider Threats So Dangerous
All in all, the root cause of insider threats are neither malware, nor viruses or system errors; those are people. Malicious activity is usually accompanied by behavioral anomalies, which makes its recognition and identification a simple task; insider menaces, however, suggest that there is a group of trusted users with legal access to the organization’s assets and, more importantly, with an understanding of where the sensitive data is located.
Thus, since it is nearly impossible to keep under control the activities of each employee involved in the work processes of an enterprise, there is a serious lack of control over the normal behavior of the user. The same goes for managing privileged user accounts withal — as they are more attractive targets for credential compromise cases, or phishing scams.
All together, it makes detecting insider threats no easy objective for security teams to accomplish.
How to Fight Insider Threats
The first thing that company owners should do about the insider security threat is to take it seriously. The next step is to make a backup plan. Make sure to choose a reputable recovery company you can resort to in case of emergency: in the event of data loss, there will be no time to seek through thousands of options at the cost of downtime for your business.
Our invariable choice is Salvagedata professional recovery lab: an old-timer of the industry that provides a full range of services, including but not limited to emergency recovery and cases of increased complexity (even those other recovery companies have claimed unrestorable). Whatever was the reason you’ve lost your important files, don’t hesitate to visit the nearest Salvagedata office, or contact the technician team for a free consultation to get your precious lost files back as soon as possible!
Now, designing a plan.
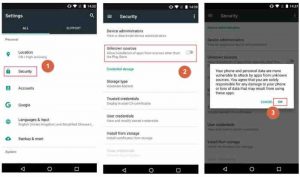
Step #1. Closing visibility gaps by aggregating security data into a centralized monitoring system is the first thing to do when it comes to effective detection of insider threats. No matter if that will be a standalone user and entity behavior analytics (UEBA), or solution security information and event management (SIEM) platform — both options will work. Start off with access, authentication and account change logs; then broaden the scope to additional information sources — say, a VPN or endpoint logs.
Step #2. Once the data has been centralized, model user behavior and assigned risk scores associated with specific perilous events (e.g. downloading to removable media, or user geography changes). Determine a baseline of normal behavior for each individual user using enough historical data.
Step #3. Compare a specific user to other employees with the same job function, and in the same location. That will help you to track deviations in user activity more efficiently: indicated behavioral anomalies will be helpful for the security team to detect if a user became a malicious insider, or if their credentials have been compromised by an external attacker. All in all, the goal is to adopt a user-focused view in order to provide your security teams with an ability to quickly detect and spot insider threat activity, and further manage user risk from a centralized location.
The overall conclusion is quite obvious: the more steps you take to ensure the security of your company sensitive data, the better you will sleep at night. Therefore, make sure you have a robust data protection strategy working on the safety of your business assets.