What Are the Best SSL Management Practices in 2020?

As technological advancements have helped the growth of businesses, they have also been plagued by cyberattacks. Data breaches have reached astronomical figures. Though the larger organisations have stringent processes in place, still there have been numerous instances in recent times. A repeat attack at Marriott has led to the compromise of 5.2 million accounts. The Dutch government reported the loss of sensitive personal information of close to 6.9 million people when they lost some hard drives.
All companies need to safeguard their websites and networks to prevent such cyberattacks. You let your guard down, and you can be in the news for the wrong reasons. Websites, be it for small businesses or large organisations, need to take the services of an SSL Certificate provider.
However, choosing a vendor and procuring the certificate is only the first step. According to Gartner, over 80% of the internet is encrypted. Still, cyberattacks take place, and it is mainly due to faulty implementation. In this article, we will discuss some of the best practices while implementing an SSL Certificate.
The certificate authority must be trustworthy
The SSL certificate utilises the HTTPS protocol that encrypts the communication between the web browser of the visitor and the web server of your website. The communication cannot be deciphered by any third-party, making it meaningless for any hacker.
While anyone can issue the certificate, it must be digitally signed to be of any use and to be recognised by web browsers. It is where the renowned Certificate Authorities come into the picture. They have a stringent approval procedure based on the type of certificate you choose. Once you fulfil these criteria, then only you receive the certificate. Web browsers have the public key of all these authorities, and you can easily spot the fake ones.
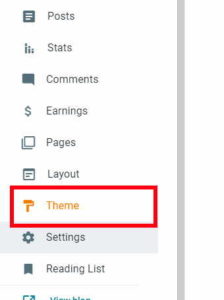
There are several certificate authorities from which you can choose. However, you must check the validity of your certificate and renew it before it gets lapsed. Also, check the hierarchy of the certificate and ensure that all the levels are valid. You must be selective when choosing your SSL Certificate provider and choose authenticate provider only.
Transfer all files to HTTPS
Installing the certificate is only a small part of the work. You will still need to transfer all the scripts, files ad images to the HTTPS platform. If you miss some of them, it could lead to the presence of mixed content. It is a mix of non-secure apart from the secure resources found on a webpage. It degrades the security, and the user experience of your website and hackers can take control over the entire webpage. Furthermore, users will not be able to access the pages with mixed content. Search engines also degrade rankings of sites with mixed content.
You can take the help of various websites that help to mark the webpages with mixed content. As a next step, you must move all these content to HTTPS. You must also take care of the plug-ins, the Javascript and Google Analytics and could be a target for cybercriminals. Also, take care of the cookies if your website uses them. They also need to be secure to prevent any misuse.
Check the certificate for viruses
Many certificates use the MD5 algorithm and could be a victim if it has a few vulnerabilities. The MD5 Hash reserves a token that can be used by hackers to obtain information about any website. It can help hackers to have unauthorised access to any website. As a safety feature, webmasters can undertake periodic checks of the SSL certificate for any prevalent vulnerability. Your IT team could finalise the periodicity. It will help to secure your certificate. Do contact the vendor if there are any issues.
Configure the SSL files on your server
Once the authority approves your request for a certificate, they will send the installation files. Your server must support the files; else you may have to convert them. Once the required certificate files are uploaded onto the server, you must pay attention to the intermediate certificate. The latest SSL/ TLS protocols must be used along with the AEAD Cipher Suites, which provides authentic 128-bit encryption support.
Protecting the private keys
The SSL certificate will need a private key to work. It is an essential asset as it is used to decrypt or encrypt the communication between the server and the connecting clients. Here, you must note that 2048-bit RSA keys are enough.
The private keys must be generated on a trusted computer. Do not get it done by any Certificate Authority. Other than using a password to protect the private key, you can also opt for hardware systems – the Hardware Security Modules. They will protect the private key even if the server is compromised. However, these are expensive too. It is essential to renew the certificate while there is time for it. And always generate a new key on receiving a new certificate.
Use of forward secrecy
Forward secrecy is a protocol that allows secure communication that is not dependent on the private key of the server. The ECDHE suites are preferred to let forward secrecy with modern browsers. It is also suggested that you use DHE suites as a fallback to the ECDHE suites.
The need for total encryption
Partial encryption is a significant lapse in security. There are sites with TLS but do not enforce encryption. Other sites mingle TLS and non-TLS content. There are also few sites with programming errors that subvert TLS. These issues can be mitigated by a single method – using encryption throughout without any exception.
Conclusion
Given the number of cyberattacks faced by organisations every year, we must always be on our guard by choosing a reliable and trustworthy SSL Certificate provider. However, only enlisting for one does not help. You must ensure utilising the best practices for implementing the certificate. We have discussed some of the best SSL management practices that could be of help.