How to Protect Your Privacy Online?
The internet and World Wide Web (WWW) are magnificent creations that revolutionized every area of our lives. Smartphones, computers, and other electronic devices create a gigantic network of machines and humans. Today, it is hard to imagine a physical world that is not interconnected by our godlike technology.
Great digital advancements have brought a lot of convenience into our lives. Oceans of information, a taxi ride, food deliveries – everything is accessible with a few clicks on your electronic device. Fast, almost instant connections and conversations with people all around the world. The Internet is an immense globalizing force that grants everyone centuries’ worth of information.
However, with Information Technologies (IT) progressing and even self-evolving at an exponential rate, the downsides of extreme digitalization start to take effect. Due to an obsession with progress and convenience, tech companies focus on collecting and processing exceedingly large amounts of user data. While some users do not mind sacrificing their privacy to enjoy a tailored product, businesses often extract much more information than the product requires. There are many instances of companies tracking their users and selling their data to third parties.
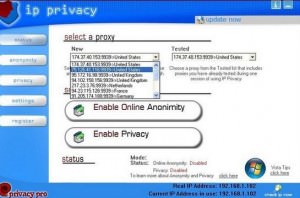
At some point, information collection reaches a stage where you feel like your privacy is in jeopardy. Big tech companies model their business model around user data aggregation either to sell or create platforms that benefit from addictive behavior. It is about time to take back our online privacy and demand the development of humane technologies. We recommend all internet users try proxy extensions as initial tools that protect network identity. A Twitter proxy can help you avoid tracking and exposure of your geolocation. Smartproxy is a great provider that offers many social media proxies for concerned clients. Let’s learn more about the best protective measures that guard our privacy and anonymity online.
Use a rotating proxy
While VPNs are effective tools to protect your online identity, over advertisement hides their limitations. There are many online tasks performed by both business and tech-savvy individuals, that greatly benefit from online privacy and anonymity. Accidental exposure of your IP address to third parties and potential cybercriminals can hurt your company or personal well-being.
Thankfully, we have rotating proxies – the best tools to hide your network identity and reinforce performed tasks. Web scraping, load balancing, social media management, and other data-oriented tasks face many obstacles that can stop any process in its tracks. If you don’t protect your privacy, then competitors and social media networks will blacklist your IP, while cybercriminals may abuse direct exposure to your address.
With a rotating proxy, you can assign a different, alternating IP to each instance of performed tasks. For example, if you plan to manage multiple social media accounts, a Twitter proxy will hide your identity while emulating a connection from any part of the world. The best rotating proxies come from residential devices and real Internet Service Providers (ISP).
Rotating proxies are legitimate tools that help us avoid exposure and activity tracking online. Finding a beginner-friendly proxy provider will help you learn the proper use of different IPs and their assignment to different applications. The proxy market is full of great providers because many companies depend on privacy protection and anonymity online.
Switch your user-agent
When you connect to the internet, a user-agent is the software that establishes an intelligible interaction with the web content. On the receiving end, every time you establish a connection with a server, usually with a browser of your choice, it will know your user-agent.
While it would make sense for websites to present the information in the same way for every user-agent, some pages deliberately change the content that is visible for web crawlers, scraping bots and other peculiar user-agents.
If you use the same user-agent for continuous connections to the website, it will know your operating system, rendering engine, browser, and other details that may be used to track you. For example, even if you use a Twitter proxy to hide your address, the social media platform may still recognize you by your browsing tendencies. Using a browser user-agent switcher with a Twitter proxy will create multiple layers of protection to your privacy online.
Internet privacy is a very sensitive subject because our laws do not control IT to create humane technologies that serve and not exploit humanity. Right now, we have a few dominant big tech companies that monopolize data and utilize information without any restriction. Ironically, if we want a free, competitive, and convenient digital environment, the internet needs governmental interference. Instead of operating for the common good, intelligent algorithms display content that appeals to our growing technology addiction, societal division, and hatred from unconfirmed, often illegitimate information sources.
In such an unpredictable digital environment, you never know how you are really tracked, so it’s a good idea to change as many things as you can and never log in to Twitter while browsing. Use a Twitter proxy and other protective tools to secure your fragile privacy online.